 Dr. Yan Tong
Dr. Yan Tong, along with Dr. Chen Li from the Mechanical Engineering department, has received a research award from the Office of Naval Research (ONR) for a research project on
"Bubble Dynamics in a Confined Domain."
As part of this project they will develop a fully automatic vision-based technique for detecting L-Vinterfaces.
Abstract:
As one of the most promising solutions to cool high power devices owing to its potentials of high heat transfer rate with a low pumping power, flow boiling has been extensively studied in the last decade. Bubble dynamics is the key to understand fundamentals of boiling heat transfer. Studies have been performed to understand transport phenomenon including evaporation during bubble nucleation and growth phase as well as condensation on bubble surface in stagnant subcooled liquid. However, bubble or vapor slug dynamics during flow boiling in microchannels after departure has not been studied. In addition, criteria of vapor bubble collapse has not been Bubble/vapor slug dynamics is governed by two important phenomena: (1) evaporation during bubble nucleation and growth phase and (2) bubble condensation in subcooled liquid. Bubble or vapor slug dynamics in a confined domain is significantly different from that in an ordinary domain due to the restriction by the channel wall. We hypothesize that bubble collapse-coalesce after departure and the physics resulting in bubble growth, shrink, collapse, and merge should be equally important to the bubble nucleation and departure, if not more important, in determining two-phase flow pattern and transport performances.
In this project, we seek to conduct systematic studies to understand the bubble/vapor slug dynamics in a confined subcooled flow boiling condition in order to better understand flow boiling in mini/microchannels or gaps. Specifically, we will experimentally and numerically study bubble departure diameter and frequency, onset of nucleate boiling, criteria of bubble collapse, and particularly, average and local liquid-vapor (L-V) interfacial heat transfer coefficient under various flow and heat transfer conditions. Accurate measurements of fluid temperature are extremely challenging, but critical to quantify important governing parameters of bubble dynamics. Two approaches will be explored and evaluated to measure average and local fluid temperature distribution. These two approaches are (1) to directly measure fluid temperature using suspended micro resistors and (2) to directly measure local fluid temperature using a nanosensor array. The nanosensors are made from encapsulated RhB fluorophores. A fully automatic vision-based technique will be developed to detect L-V interfaces and to estimate the motion of the interface by non-rigid image registration and onsite-calibration. This vision-based technique is essential to reduce massive data from high-speed optical images to assure a consistent data reduction process.
The knowledge obtained through this project will greatly extend knowledge of two-phase transport at the microscale and would be critically important in further advancing a number of emerging technologies, such as micro-heat exchangers, microfluidic thrusters, microbubble-driven pumps, and microfluidic logics. More importantly, the success of this fundamental research will advance theoretical base in realizing promising two-phase cooling technologies. This will accelerate the development of highly efficient two-phase cooling technologies to manage waste heat for DoN high power sensors and weapon systems and therefore to enable superior defensive/offensive capabilities of the next generation warships.



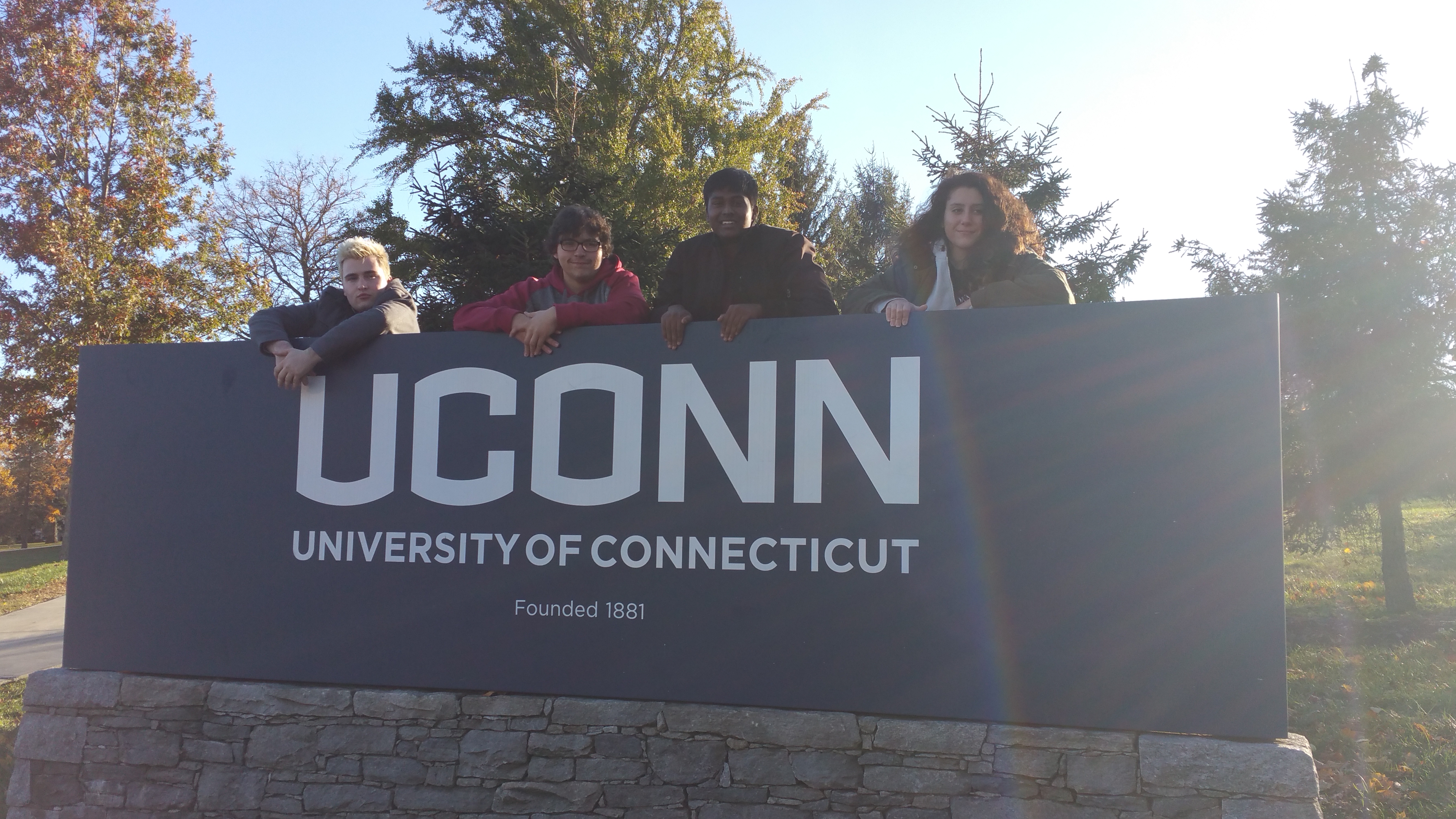
 We recently hosted a third grade class field trip for students from Saint Joseph Elementary School. They asked lots of great questions as they learned about human-robot interaction from Dr. Jenay Beer, as you can see.
We recently hosted a third grade class field trip for students from Saint Joseph Elementary School. They asked lots of great questions as they learned about human-robot interaction from Dr. Jenay Beer, as you can see.



 We would like to welcome our newest faculty member
We would like to welcome our newest faculty member