Edward Sitar: CRA Outstanding Undergraduate Researcher Award Finalist
We are proud to report that Edward Sitar, has been selected as a Finalist for the 2023 CRA Outstanding Undergraduate Researcher Award. This award program recognizes undergraduate students in North American colleges and universities who show outstanding research potential in an area of computing research.
Alumnus Spotlight: Manas Gaur
 “It was a very fascinating experience for me, in terms of the collaborations I was able to develop within a short span at USC,” says Dr. Manas Gaur who received a doctorate in computer science in August. Within a year of arriving in Columbia, he was given the opportunity to present his research at the Annual Computing Conference at the SEC Meeting. He was also a part of large team-based National Science Foundation (NSF) and National Institutes of Health (NIH) grants with professors at USC.
“It was a very fascinating experience for me, in terms of the collaborations I was able to develop within a short span at USC,” says Dr. Manas Gaur who received a doctorate in computer science in August. Within a year of arriving in Columbia, he was given the opportunity to present his research at the Annual Computing Conference at the SEC Meeting. He was also a part of large team-based National Science Foundation (NSF) and National Institutes of Health (NIH) grants with professors at USC.
Outside of his research, Gaur has tutored high school, undergraduate and graduate students from different backgrounds and institutions. He credits a fellowship at University of Chicago, where he was an Eric and Wendy Schmidt Data Science for Social Good Fellow in 2017, for his interest in giving back. In 2019, he received an AI for Social Good Fellowship from Dataminr Inc.
Read the full article at Artificial Intelligence, real application
AIISC Event Posters and Photos
AIISC's 1st Retreat last Friday was hugely successful. Over 50 in attendance engaged in active discussions over 23 student posters representing a subset of the topics our ~40 researchers work on, attended the panel in which our collaborators shared their views on "AI in your research" and continued conversations over breakfast and lunch.
Please check out the posters and the photos of this vibrant event, and visit our LinkedIn page followed by over 8600 worldwide.
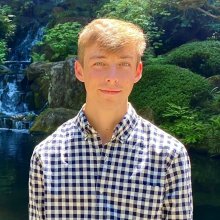
Accurate Human Silhouettes and Body Joints Estimation from Commodity 5G Millimeter-Wave Devices
The need for understanding and perceiving at-home human activities and biomarkers is critical in numerous applications, such as monitoring the behavior of elderly patients in assisted living conditions, detecting falls, tracking the progression of degenerative diseases, such as Parkinson’s, or monitoring recovery of patients’ during post-surgery or post-stroke. Traditionally, optical cameras, IRs, LiDARs, etc., have been used to build such applications, but they depend on light or thermal energy radiating from the human body. So, they do not perform well in occlusion, low light, and dark conditions. More importantly, cameras impose a major privacy concern and are often undesirable for users to install inside their homes.
Now a team of researchers from the Systems Research on X laboratory at the University of South Carolina has designed a monitoring system, called MiShape, based on millimeter-wave (mmWave) wireless technology in 5G-and-beyond devices to track humans beyond-line-of-sight, see through obstructions, and monitor gait, posture, and sedentary behaviors. This system provides an advantage over camera-based solutions since it works even under no light conditions and preserves users’ privacy. By processing mmWave signals and combining them with custom-designed conditional Generative Adversarial Networks (GAN) model, they demonstrated that MiShape generates high-resolution silhouettes and accurate poses of human body on par with existing vision-based systems.
The findings are reported recently in the ACM Journal on Interactive, Mobile, Wearable and Ubiquitous Technologies (IMWUT) in a paper co-authored by UofSC graduate students, Aakriti Adhikari and Hem Regmi, and UofSC faculties of computer science and engineering department, Dr. Sanjib Sur and Dr. Srihari Nelakuditi. It was also recently presented at the highly selective international conference, ACM UbiComp 2022, by Aakriti Adhikari.
In their proposed approach, they first train a deep learning model based human silhouette generator model using mmWave reflection signals from a diverse set of volunteers performing different human poses, activities, etc., and then run the model to predict the silhouette of unknown subjects performing unknown poses, which are not part of the training process. The silhouette can then be used to generate a body skeleton, which can be tracked continuously, even under obstructions or low-light, for monitoring human activities automatically. Furthermore, the system can generalize to different subjects with little to no fine-tuning.
This research is an example of an emerging paradigm called Sensing for Well-being. It enables ubiquitous sensing techniques so that devices and objects become “truly smart” by understanding and interpreting the ambient conditions and activities with high precision, without relying on traditional vision sensors. “Through experimental observations and deep learning models, we extract intelligence from wireless signals, which, in turn, enable ubiquitous sensing modalities for various human activities and silhouette generation,” says Prof. Sur. The authors are also collaborating with researchers from the Arnold School of Public Health and doctors from the School of Medicine to bring these technologies to practice. Another application of this work is in monitoring human sleep quality and postures with ubiquitous networking devices, such as next-generation wireless routers at home. “We can use mmWave wireless signals to automatically classify, recognize, and log information about sleep posture throughout the night, which can provide insights to medical professionals and individuals in improving sleep quality and preventing negative health outcomes,” Sur says.
The research was supported by the National Science Foundation, under the grants CNS-1910853, MRI-2018966, and CAREER-2144505, and by the UofSC ASPIRE II award.
Helping people manage their diet using AI models

In recent years, people have become more aware of their dietary choices and the impact of food on health and chronic diseases. Revathy Venkataramanan, a computer science and engineering Ph.D. student, is using artificial intelligence (AI) techniques to develop nutritional analysis from food images and meal recommendations based on a user’s health conditions and food preferences.
Read the full article here.
CSE Faculty Research Awards
We are proud to report that several of our faculty members have received research awards. They are:
- Dr. Pooyan Jamshidi received an NSF grant for his research "Collaborative Research: EAGER: Towards a Design Methodology for Software-Driven Sustainability"
- Dr. Forest Agostinelli received a grant from NASA EPSCoR for the project "Radiation Hard and Machine Learning Reinforced 4H-SiC Radiation Detectors for Space Applications"
- Dr. Csilla Farkas was given a Department of Defense grant as part of the "2022 DoD CySP Grant Program"
- Dr. Yan Tong received an NSF grant for her research "Transient Behavior of Flow Condensation and Its Impacts on Condensation Rate."
- Dr. Homayoun Valafar received an NIH-NIGMS grant for the project "South Carolina IDeA Networks of Biomedical Research Excellence (SC INBRE) - Bioinformatics Core (BIPP)"
Generative Discovery of New Semiconductors: Design without Understanding
 Discovery of novel materials with exceptional properties is fundamental to the technology progress to more efficient solar panels, longer-life batteries, and room-temperature superconductors. Traditionally, the discovery process is a highly ad hoc, empirical, serendipitous process based on inventors’ ingenuity and knowledge. To address this issue, materials scientists now mainly resort to the rational design process, in which they aim to obtain a mechanistic understanding of how materials composition and structures determine their function properties. However, the complexity of these relationships and the difficulty to enumerate all the delicate and intricate design rules makes it challenging to explore the vast chemical design space using such rational design approaches.
Discovery of novel materials with exceptional properties is fundamental to the technology progress to more efficient solar panels, longer-life batteries, and room-temperature superconductors. Traditionally, the discovery process is a highly ad hoc, empirical, serendipitous process based on inventors’ ingenuity and knowledge. To address this issue, materials scientists now mainly resort to the rational design process, in which they aim to obtain a mechanistic understanding of how materials composition and structures determine their function properties. However, the complexity of these relationships and the difficulty to enumerate all the delicate and intricate design rules makes it challenging to explore the vast chemical design space using such rational design approaches.
Now a team of researchers from the Machine Learning and Evolution Laboratory at the University of South Carolina applied a paradigm-shifting deep learning based generative design approach for computational discovery of novel semiconductors. By combining a generative adversarial networks (GAN) model, a metal classifier, and high-throughput first-principles calculations, they have discovered 12 novel stable AA’′MH6 semiconductors in the F-43m space group. They showed that AA′MnH6 and NaYRuH6 semiconductors have considerably different properties compared to the rest of the AA′MH6 semiconductors, which are all wide-bandgap materials and may be ideal for certain applications.
The findings are reported today in the journal Nature npj Computational Materials, in a paper by UofSC postdoc Edirisuriya M. Dilanga Siriwardane, graduate student Yong Zhao, and UofSC Professor of Computer Science Dr. Jianjun Hu (the corresponding author); Indika Perera at the University of Moratuwa.
In their generative design approach, they first train a deep neural network based crystal structure generator model using all known crystal materials deposited in the databases, and then they run these generators to create a large number of hypothetical materials, which are then fed to the metal classifier to filter out potential semiconductors. Then the top candidate structures are fed to the first principle simulation software Vasp for structure relaxation and stability check, and property calculation, which are very slow processes that used the High Performance Clusters (HPC) at the UofSc Research Computing facility.
This work is another success case for the emerging AI-for-Science paradigm conducted by the interdisciplinary team with the computational materials expertise from Dr. Siriwardane and deep learning and computing expertise from Dr. Zhao, Prof. Hu, and Prof. Perera. “Compared to rational design approaches, the deep learning based generative design approach has the special advantage in terms of its capability to efficiently navigate the almost infinite chemical design space of materials, assisted by the implicit, latent, dark knowledge learned by the neural network”, says Prof. Hu. Their new material design approach does not require explicit specification of design knowledge and rules (so, design without understanding), which is in sharp contrast to the traditional rational design methods.
“The deep learning generative models are very good at learning implicit chemical and materials composition knowledge”, says Dilanga, the paper’s lead author. “But the current algorithm can be further improved in terms of their success rates of generating stable structures”. Since the DFT quantum simulation is very slow, it is desirable to have a high hit-rate when they are used for validating the generated hypothetical materials. He adds, “our capability to discover more interesting materials is currently also limited by the computing power at UofSC”.
“Generating thermodynamically and structurally stable crystals structures is a non-trivial problem”, says Zhao, who led the development of the deep generative algorithm. He has recently introduced physical rules and geometric constraints to further improve the quality of the generated crystal structures.
For the discovered materials to become practical on the market or be adopted commercially, Hu says, “our hypothetical materials can guide experimental materials scientists to synthesize and characterize their properties”.
The research was supported by the National Science Foundation and used the HPC computing facility of UofSC.
CSE Faculty Research Awards
We report that six of our faculty members have received research awards. They are:
- Dr. Qi Zhang received a grant from the National Science Foundation (NSF) for "Cooperative Planning and Learning via Scalable and Learnable Multi-Agent Commitments"
- Dr. Mike Huhns and Vignesh Narayanan received award from the University of Maryland/ARLIS/DOD for their project "Information Competition Simulator"
- Dr. Ramtin Zand received an award from the Findora Foundation for the project "Design and Implementation of Hardware Accelerator for Gemini Zero-Knowledge Protocol"
- Dr. Jason Bakos received an award from the National Science Foundation (NSF) for the project "Machine Learning on the Edge for Real-Time Microsecond State Estimation of High-Rate Dynamic Events”
- Dr. Biplav Srivastava received a grant from the South Carolina Research Authority (SCRA) for the project "AI-assisted Data-driven team building for individual and institutional success"
- Dr. Yan Tong received an award from the SC Space Grant Consortium/College of Charleston/NASA for the project "Computational Algorithms and Speed: An Education Game for High School Students (Andrew Bernhardt)”
Harnessing the Power of Artificial Intelligence
The article Harnessing the power of artificial intelligence highlights the research of several of our research faculty.
Dr. Pooyan Jamshidi Receives Breakthrough Award

Dr. Pooyan Jamshidi has received a UofSC Breakthrough Award for his reasearch in robotics, artificial intelligence and machine learning. You can read the full story here.
Scholarship for Current Students – Deadline extended - Apply now!
The John H. Fain scholarship provides an incentive for upper level Computer Information Systems (CIS) and Computer Science (CS) majors to become entrepreneurs. Fain scholars may receive up to a total of $5,000. View eligibility requirements and apply here.
CSE Faculty Research Awards
We report that three of our faculty members have received research awards. They are:
- Dr. Biplav Srivastava: from Tantiv4, Inc for "Task Order 6: Analysis of Power IoT data for management of infrastructure".
- Dr. Amit Sheth: from UK Research and Innovation/Queen Mary University London for "Alan Turing Institute’s Turing AI Fellowships".
- Dr. Srihari Nelakuditi from then National Institute of Diabetes and Digestive and Kidney Diseases (NIDDK)/NIH for "Validity and Utility of Consumer-based Wearable Fitness Trackers to Monitor Free-Living Physical Activity Energy Expenditure and Sleep in Children 5-12 Years Old".
- Dr. Homay Valafar and Forest Agostinelli from the UofSC Office of Research for “ASPIRE II: Automatic and personalized identification of smoking using smartwatches".
Magellan Scholars Summer and Fall 2022
We congratulate the following Computer Science and Engineering undergraduate students for receiving a Magellan Scholar Award for Summer and Fall 2022. Their names and projects are:
- Ahad Chattha, "Development of Mitral Valve Disease induced by TGFB1 Signaling"
- Thomas Geiger, "Mapping Per- and Polyfluoroalkyl Substances (PFAS) in South Carolina Rivers: Are There Hotspots?"
- Dylan Johnson, "Graph Constrained Crystal Structure Prediction Using Neural Dynamics"
- Lilian Lamb, "A self-positioning platform for stationary measurements in the aquatic environment"
- Jacqueline Schellberg, "Millimeter-Wave Imaging on 5G Handheld Smart Devices"
- Katelyn Wyandt, "AI-Driven User Interface Design for Optimal User Engagement: A Use Case for Personalized Learning"
- Zachary Young, "Generating Global Indoor Point Clouds Using 5G Millimeter-Wave Technology"
Discover UofSC Day: CSE Honorees
The following CSE undergraduates were recognized for their posters on research, education, and public service at Discover UofSC 2022:
- James Seekings, Computer Science (major), Mathematic (major) - Junior
- Sara Hendrix, Computer Science (major) – Freshman
- Xeerak Muhammad, Computer Engineering (major) - Senior
- Antonio Turner, Computer Engineering (major) – Sophomore
- Lilian Lamb, Computer Engineering (major) – Sophomore
Hendrix and Seekings Win First Place at UofSC Discover

 Dr. Zand is excited to share that two of iCAS Lab's undergraduate students, Sara Hendrix and Blake Seekings, and their Ph.D. mentors, Peyton Chandarana and Mohammadreza Mohammadi, received the First Place Award in the Engineering and Computing track at UofSC Discover for their work on "Static American Sign Language Recognition Using Neuromorphic Hardware."
Dr. Zand is excited to share that two of iCAS Lab's undergraduate students, Sara Hendrix and Blake Seekings, and their Ph.D. mentors, Peyton Chandarana and Mohammadreza Mohammadi, received the First Place Award in the Engineering and Computing track at UofSC Discover for their work on "Static American Sign Language Recognition Using Neuromorphic Hardware."